Catch the phish before you click!
A common way cyber criminals gain access to valuable information at universities is through deceptive emails known as “phishing” messages.
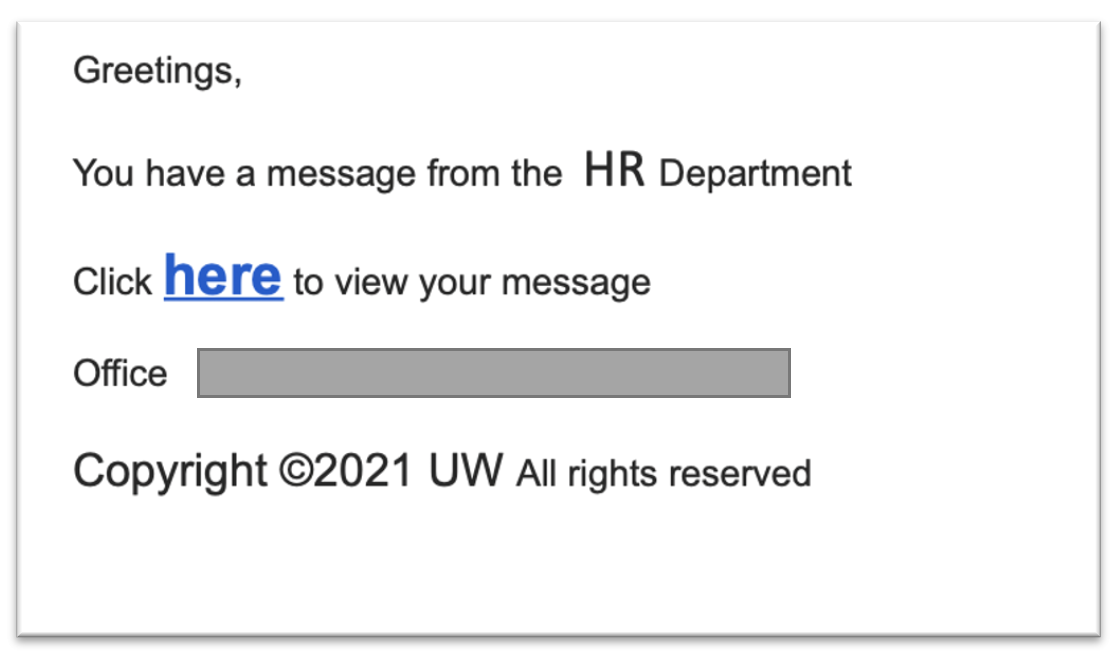
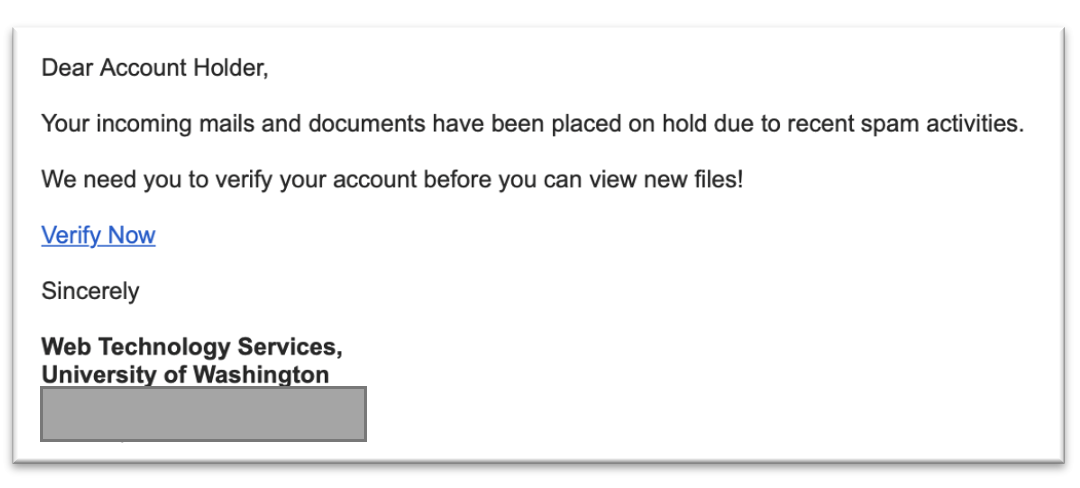
Below are examples of recent phishing campaigns. If you receive an email that asks you to download an attachment or enter your UW NetID credentials, send the message as an attachment to help@uw.edu.
Recent Catches
(Click on each example to zoom)
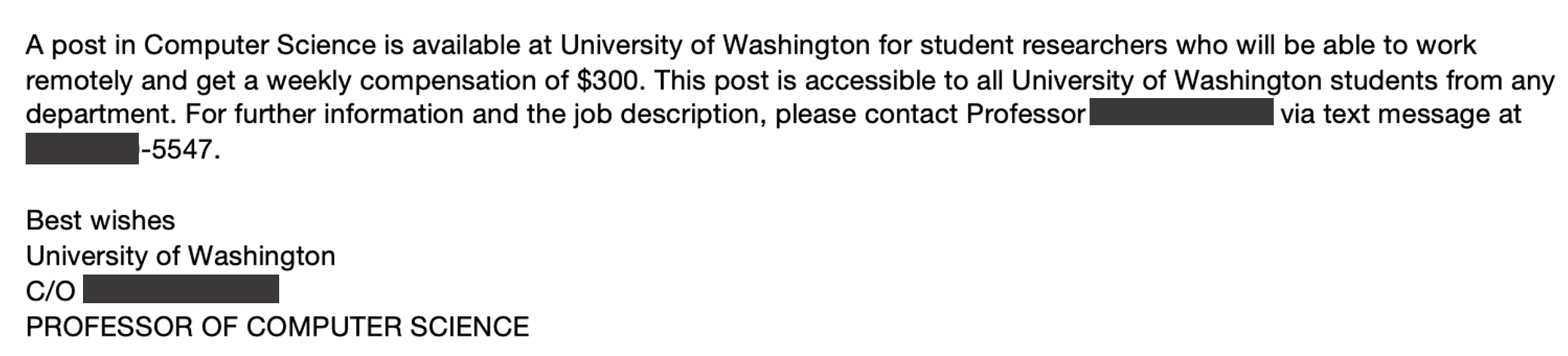
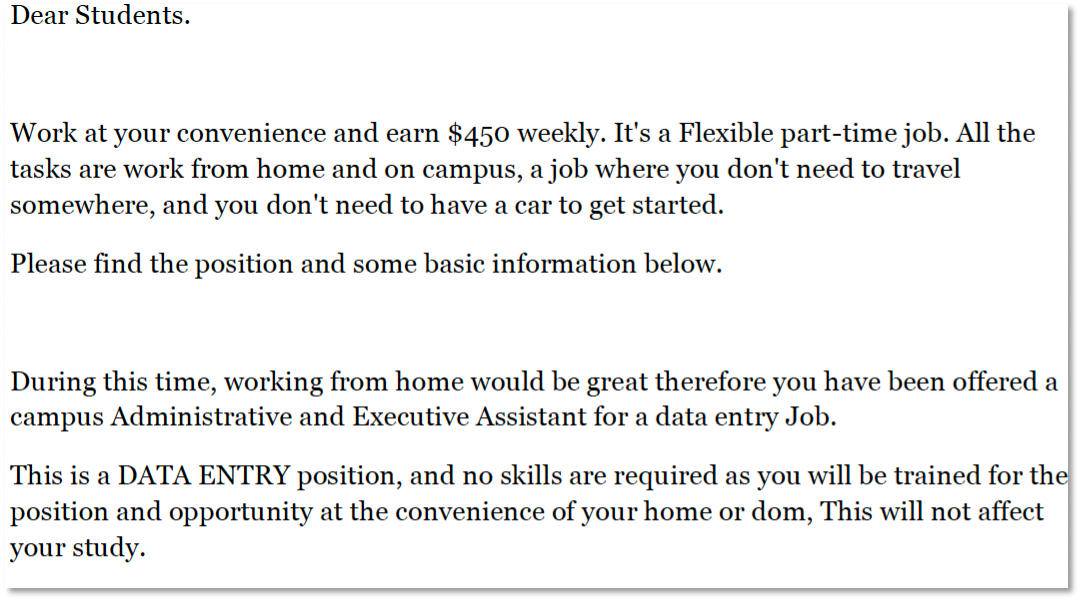
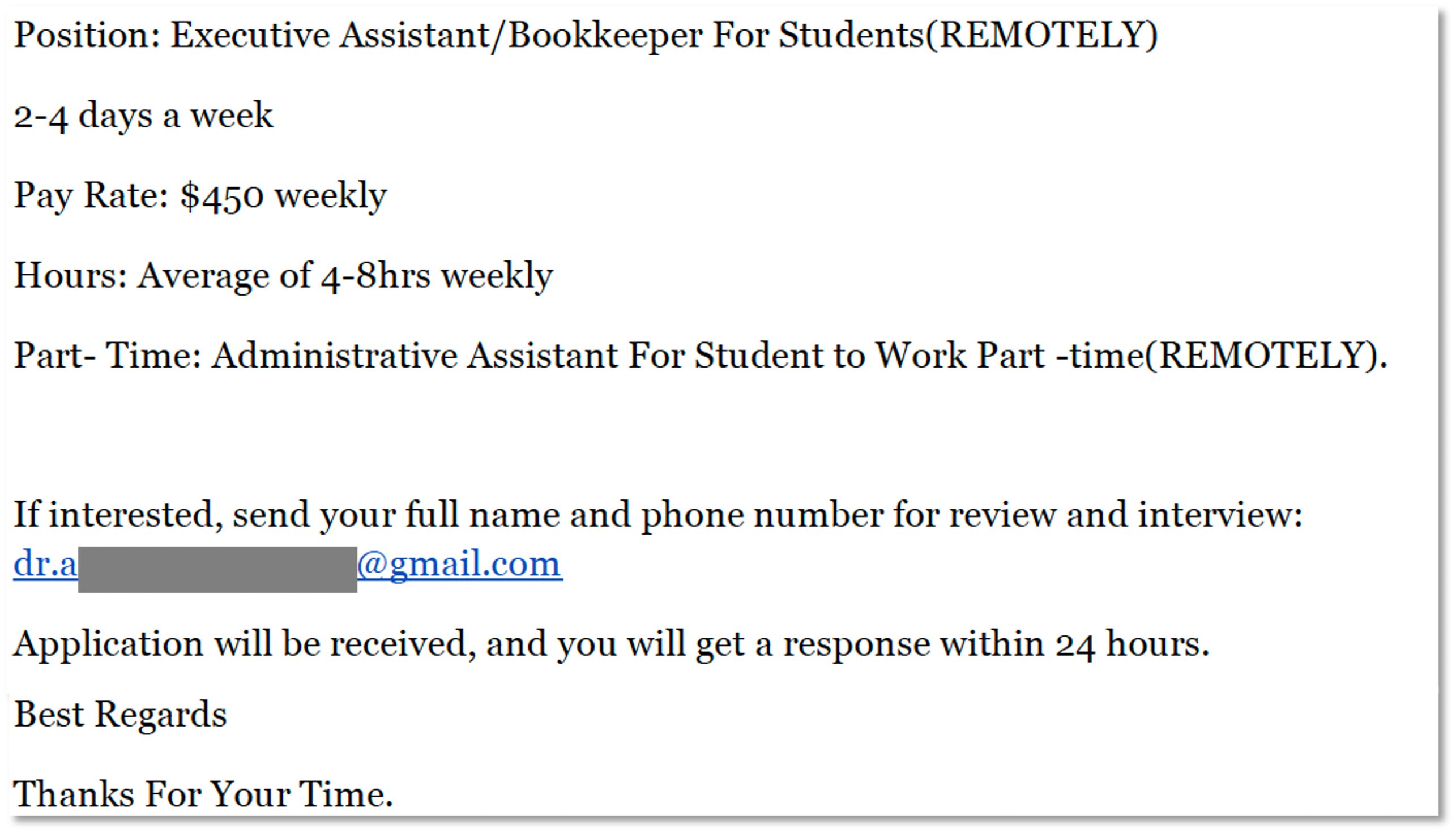
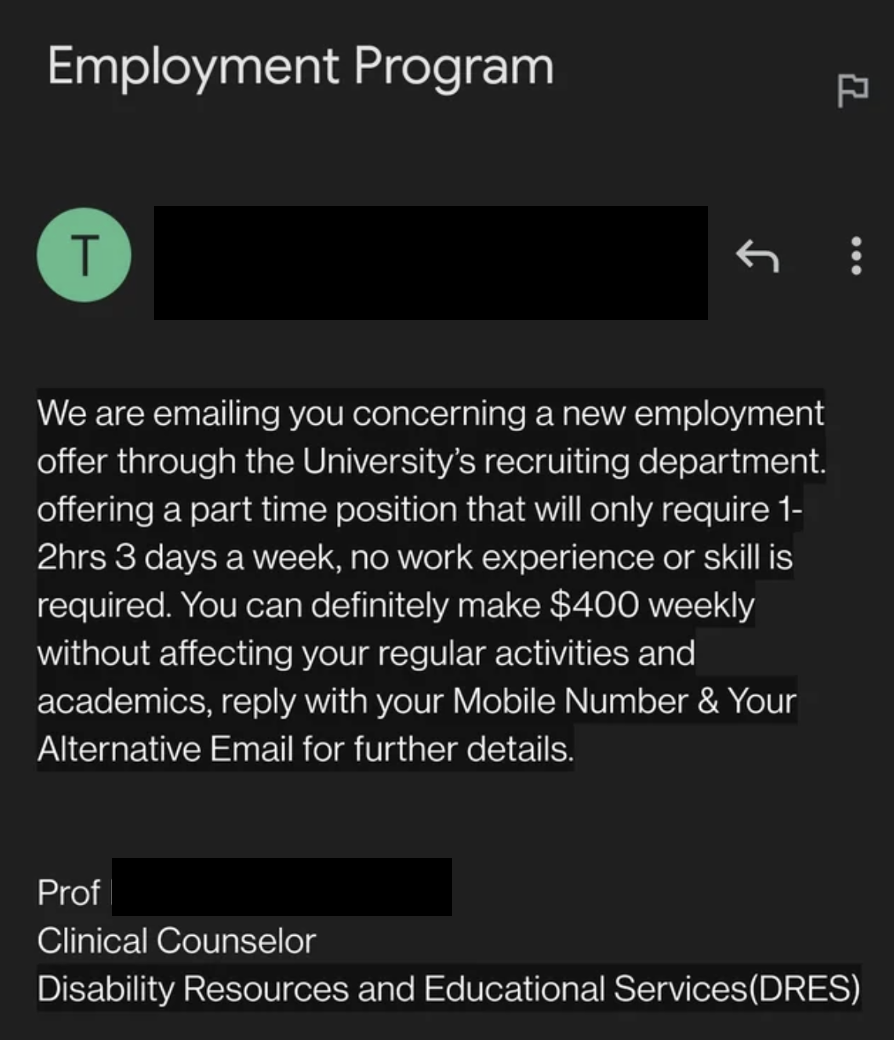
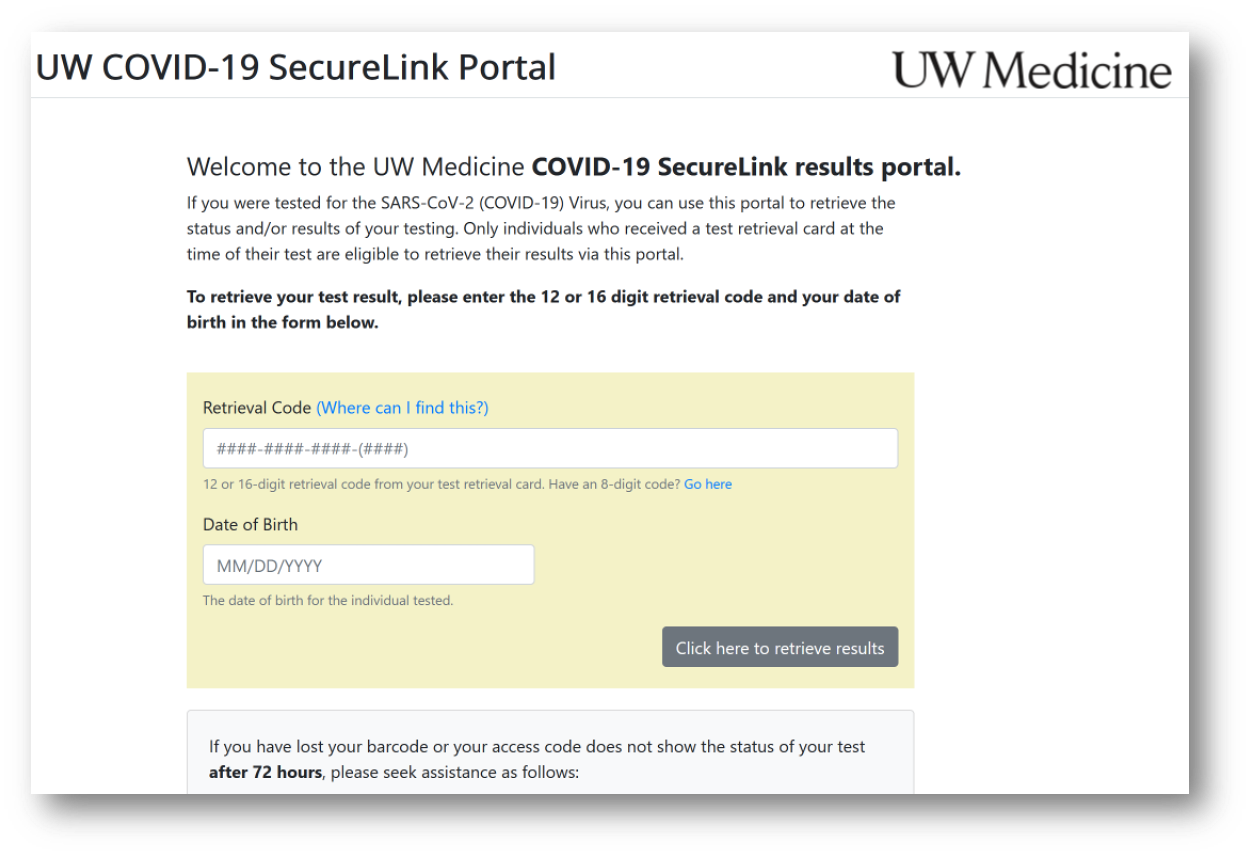
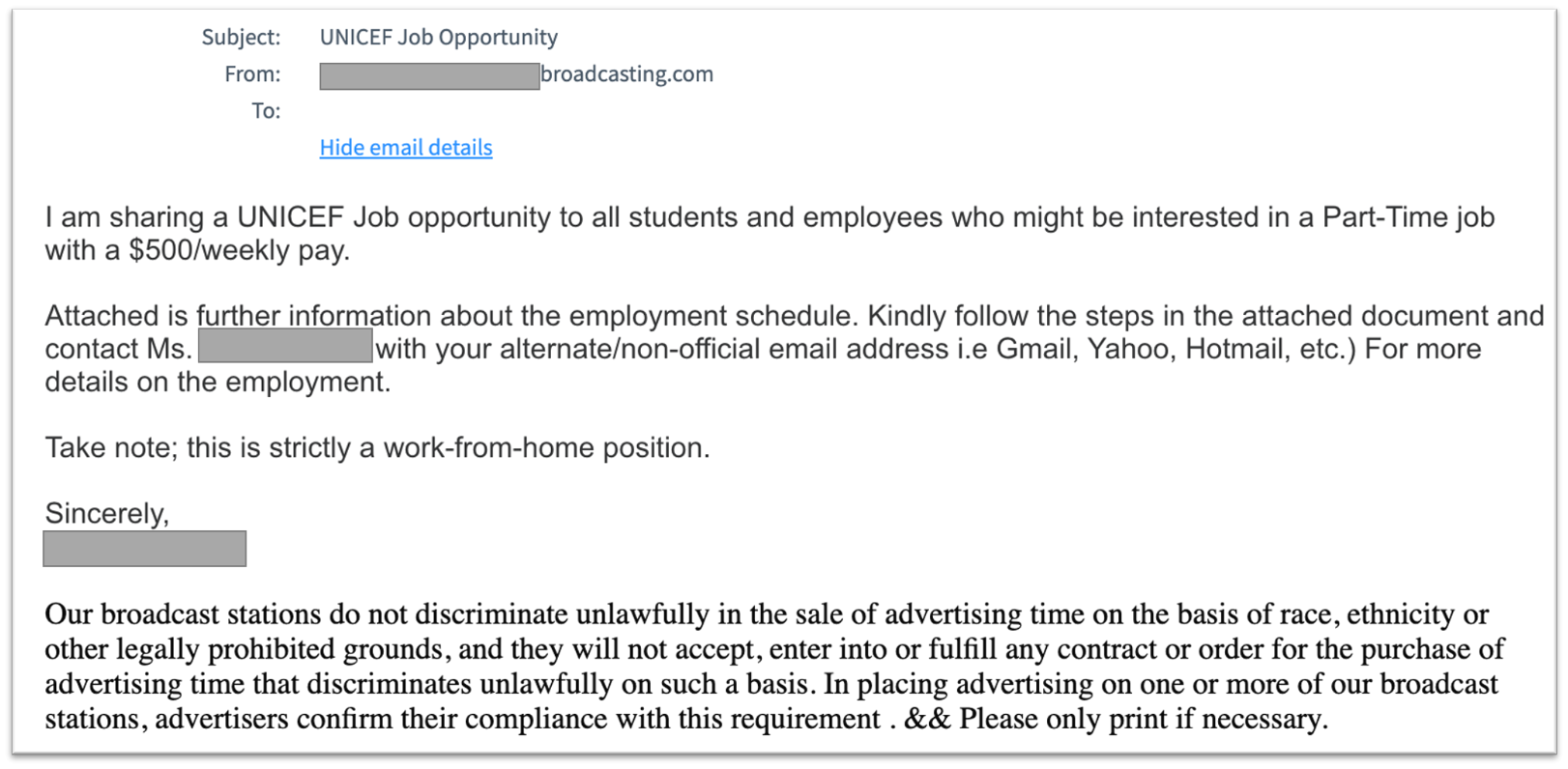
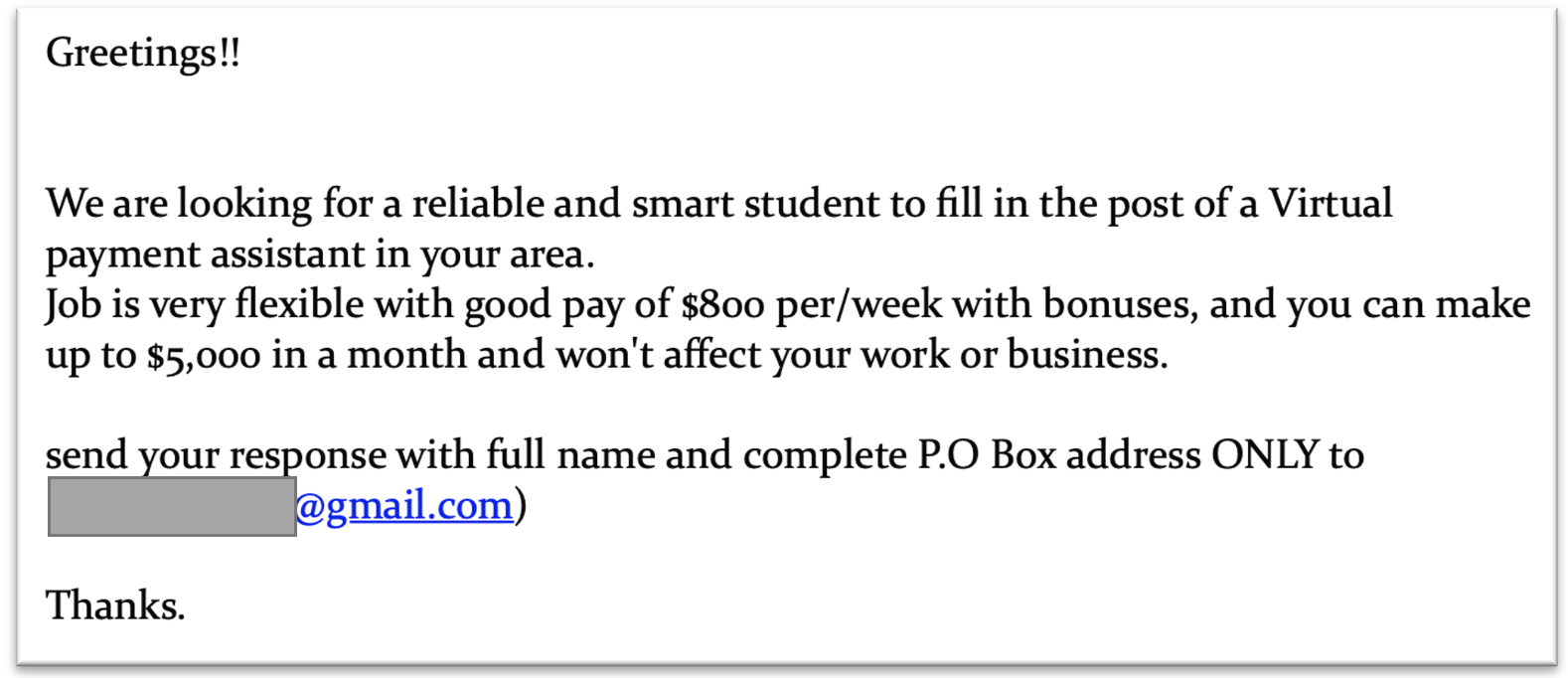
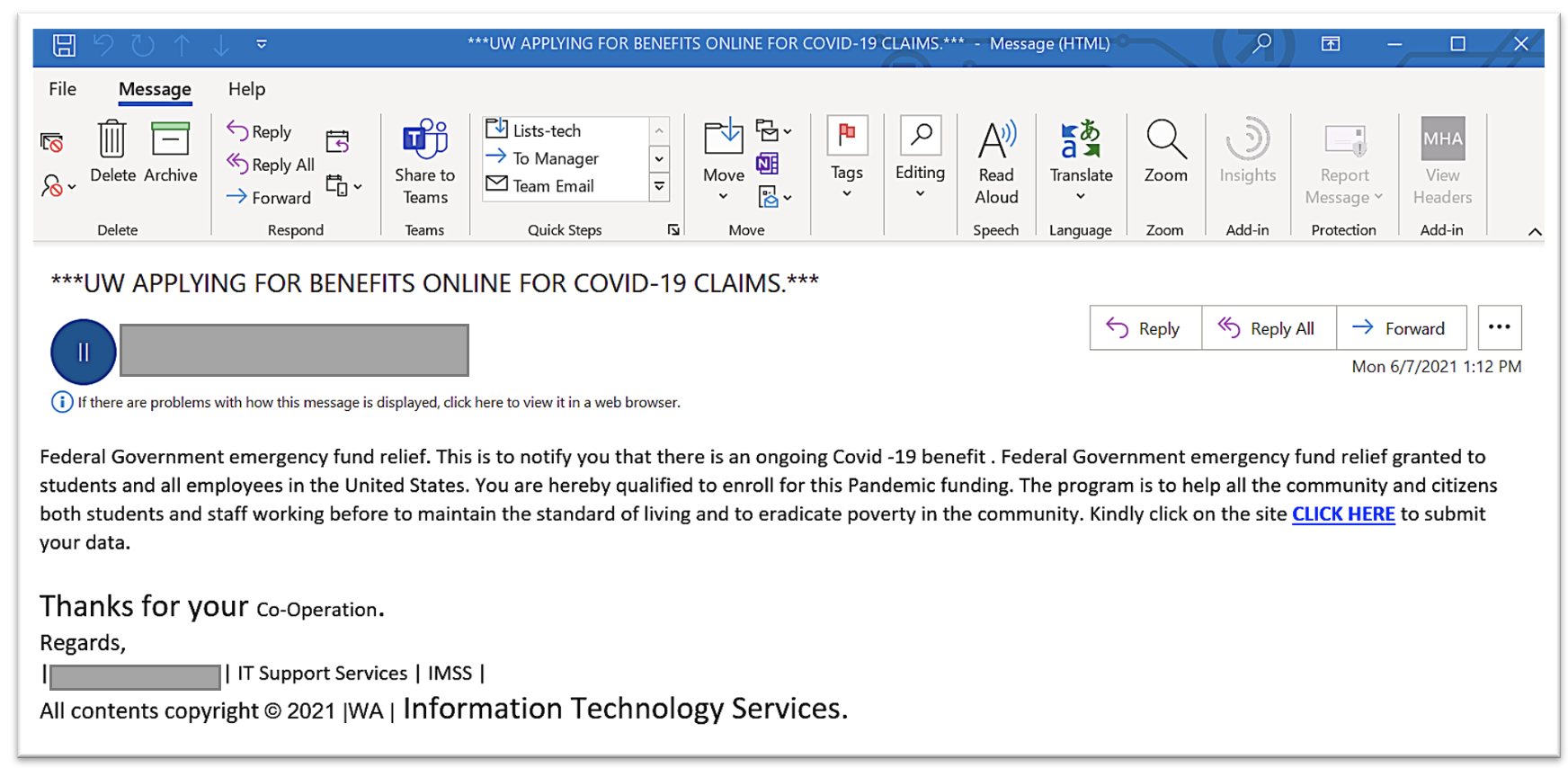
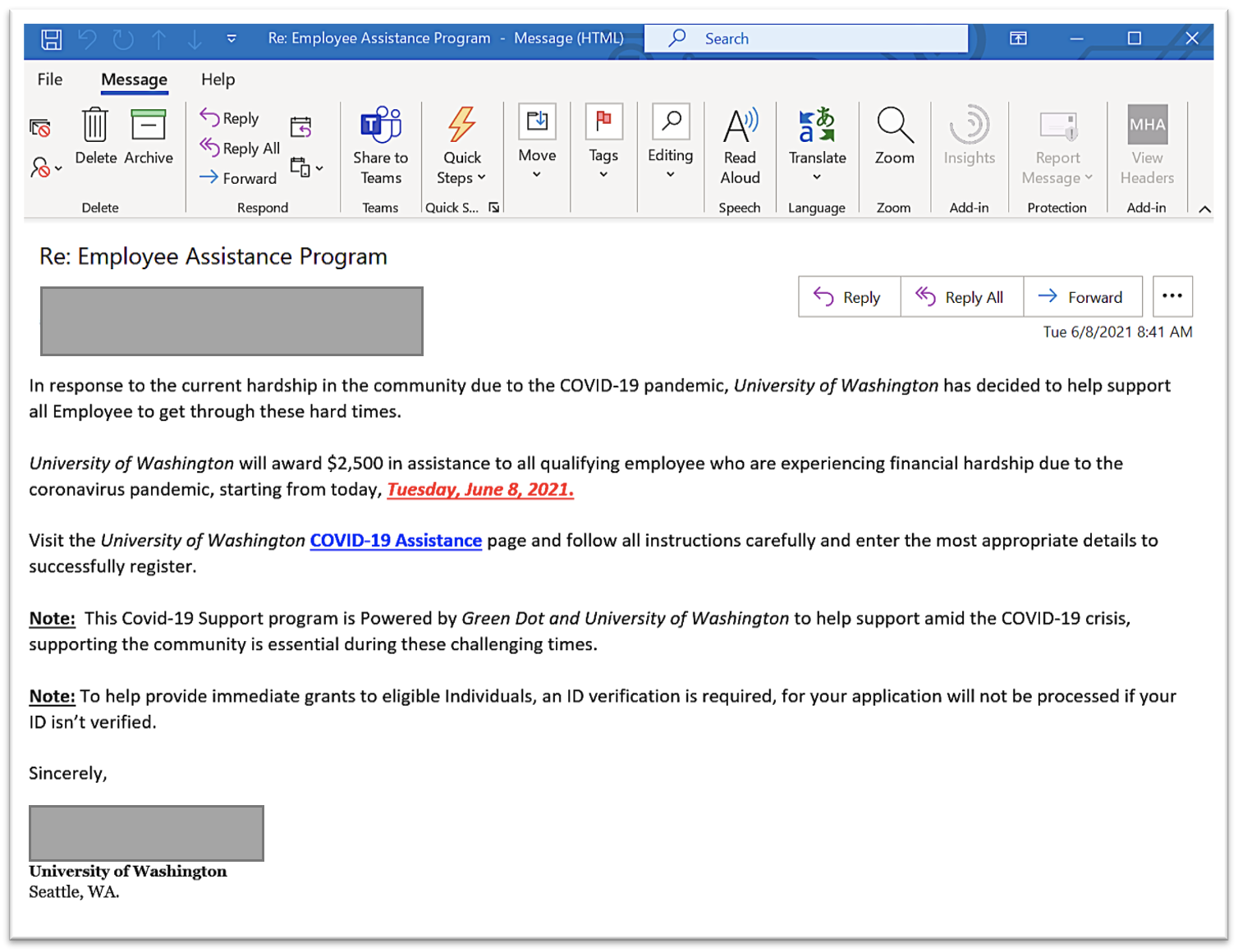
The following two images are a scam targeting UW students:
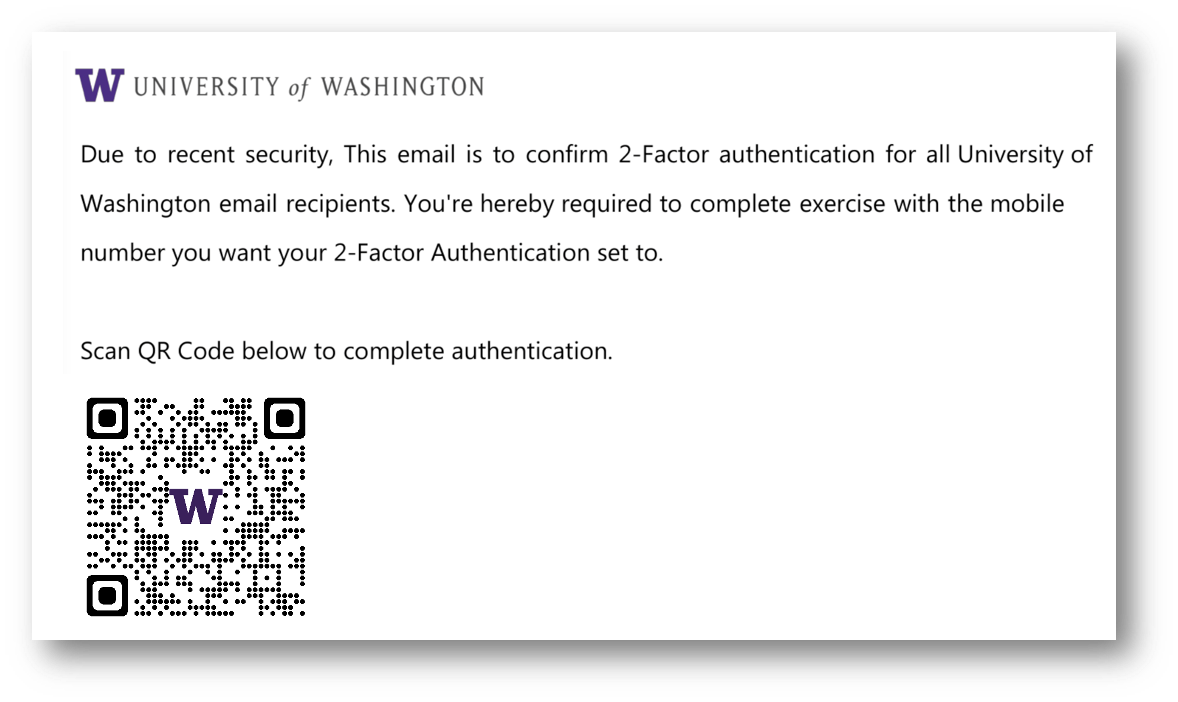
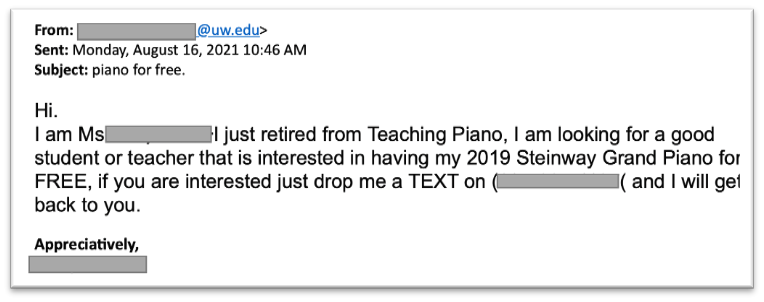
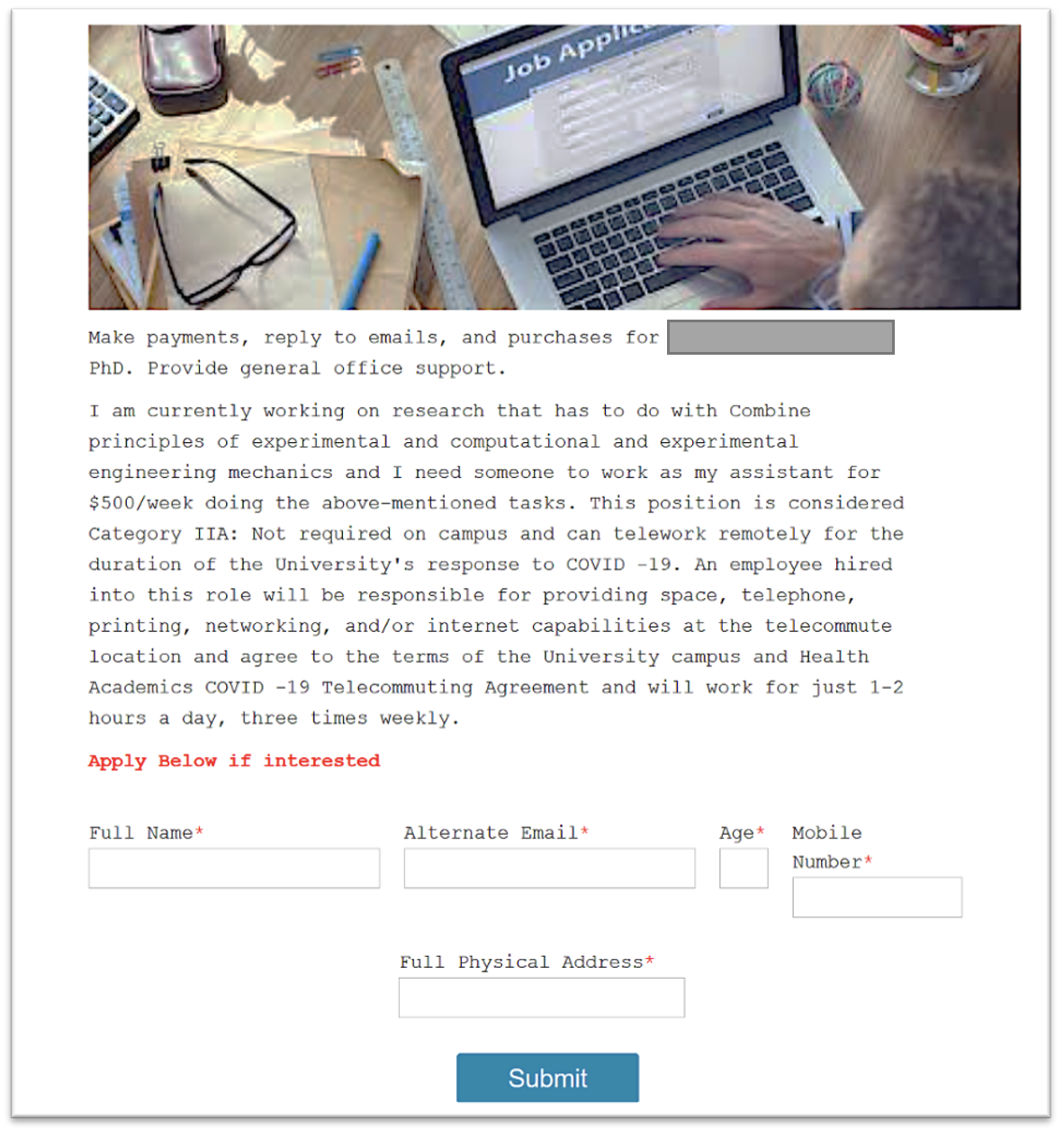
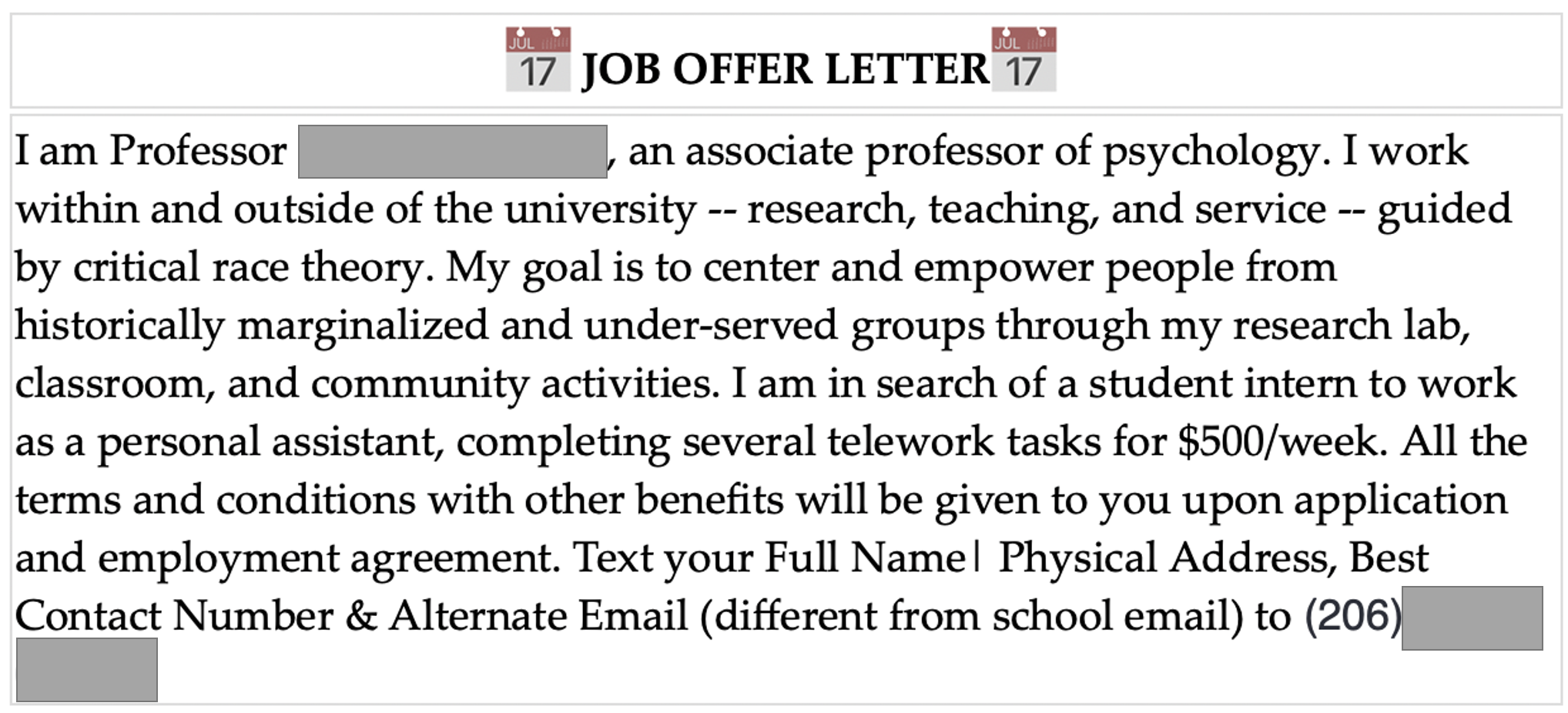
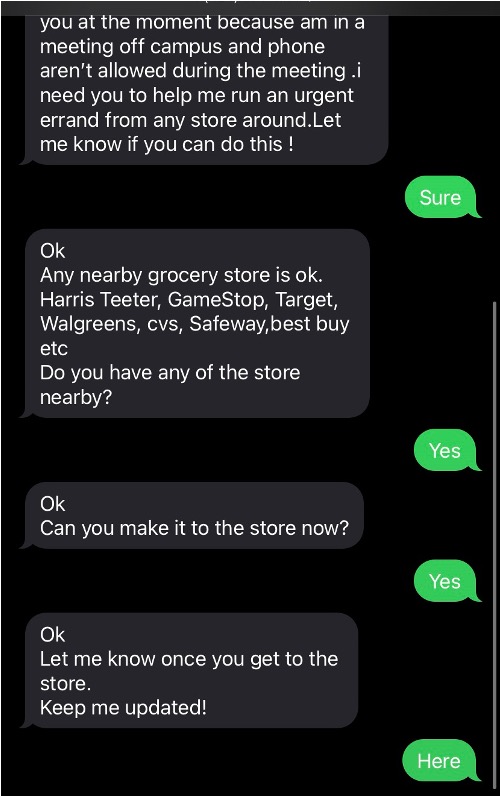
Often gift card scammers will pose as someone you know and then ask you to switch from email to text:
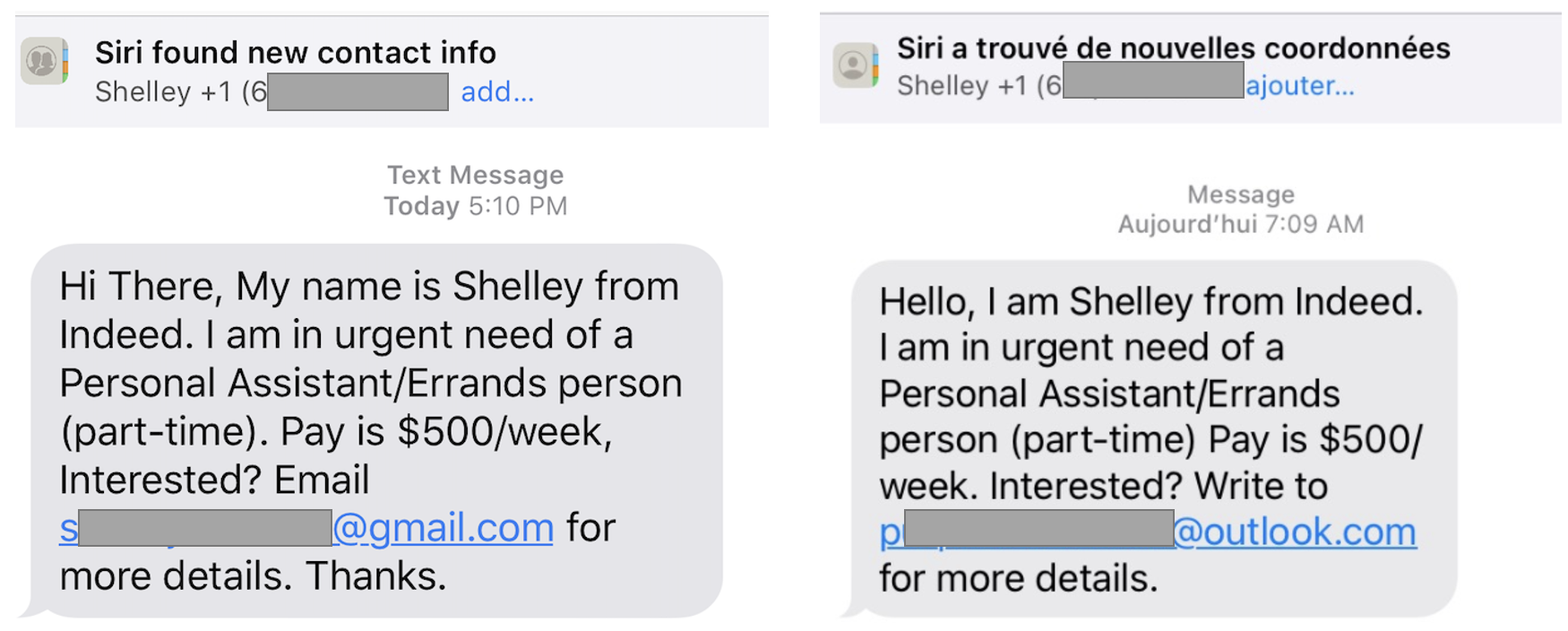
A pair of texts sent to UW students recently:
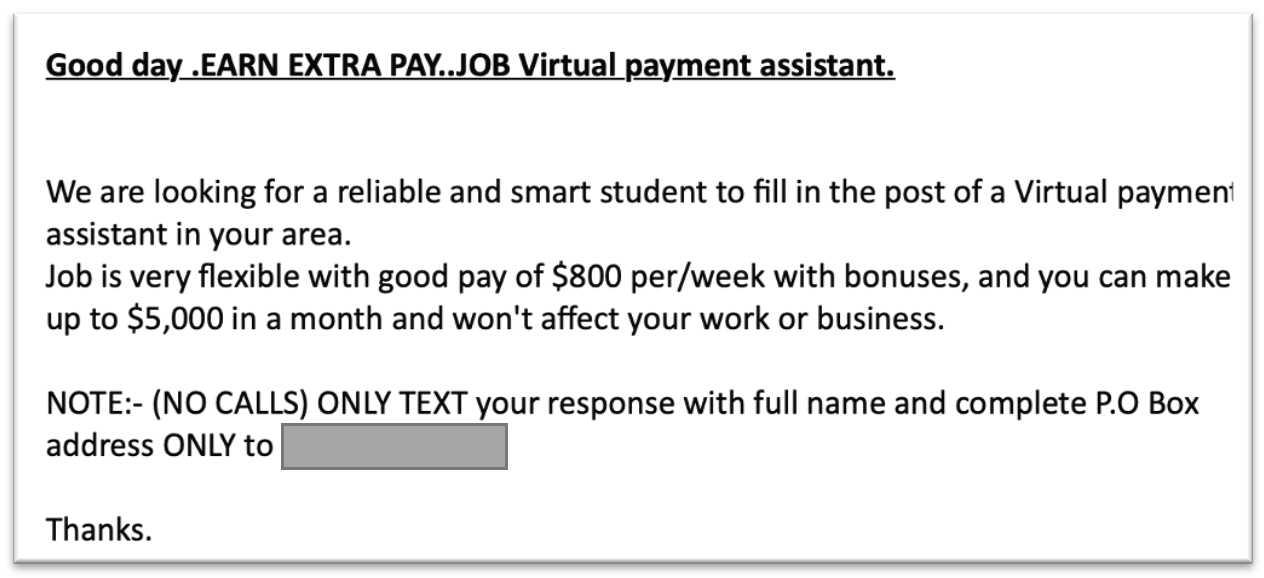
Gift Card Scam
UW continues to see “Are you available?” scam messages. These are usually org-chart related in that a supervisor is impersonated on messages sent to staff in their departments or colleges. The goal of the criminal sending the message is to convince the recipient to buy some gift cards, which are difficult to trace and easy to spend. The scammer may try to carry out the conversation via email or text message if the victim provides a cell phone number.
Please report any of these messages to security@uw.edu
Spam vs. Phish – what’s the difference?
Spam is unsolicited email, typically sent to a widespread audience, that is usually from someone who is trying to get you to buy something.
A phishing email is a type of spam in which the sender tries to get you take a specific action, such as:
- Clicking on a link
- Entering your UW NetID credentials
- Downloading an attachment
The goal is to either load malicious software (aka malware) onto your computer or device, to steal your UW login credentials to access UW data and resources, or to use those credentials to send more spam.
How to report a phish that specifically targets the UW
If you receive an email in which someone is trying to get you to download an attachment or enter your UW NetID and password onto a fake web page, send the email as an attachment to help@uw.edu.
UW Medicine employees should cc uwmed-abuse@uw.edu.
If you receive an email in which someone tries to sell you a product (such as cheap medication), forward the message to reportedspam@cac.washington.edu.
Other UW Phishing Resources
Infographic
Risk Advisory and Best Practices
Online training video
Messages to the UW Community
Protecting Your Email – IT Connect (UW-IT website)